The fundamentals of cryptography, its significance, and its present purposes in cybersecurity are the topic of this blog submit. This weblog aims to break down the fascinating field of cryptography by offering an in-depth take a glance at its fundamentals and how they can be utilized in cybersecurity. Have you ever puzzled how your bank particulars keep safe during online transactions or how companies defend sensitive knowledge explain cryptography from cyber threats? In an increasingly digital world, information safety isn’t simply an IT concern—it’s a enterprise imperative. As the demand for cybersecurity experts rises, understanding cryptography’s which means becomes not only relevant however essential for professionals across sectors. The main kinds of cryptography are symmetric encryption, asymmetric encryption, and hash capabilities.
If we go by the literal meanings of the time period – the prefix “crypt” signifies “hidden” and suffix “graphy” implies “writing”. These Days, the Tech world is flourishing and with that, is the data that is being transferred, stored, and exchanged on the web. Privateness has become fairly a important side however is now scarce to implement. Nonetheless, there are some strategies that can be enforced to guarantee that personal and secured communication is established within the network. Cryptographic algorithms work by manipulating information in a means that’s troublesome for unauthorised events to reverse or decipher. The choice of algorithm is dependent upon the particular requirements of a cryptographic application, in addition to the specified degree of security.

This algorithm makes use of a pair of keys, one to encrypt and one other to decrypt. This means Non-fungible token, senders and recipients don’t need to share the cipher with each other. Instead, an algorithm creates a pair of keys and sends one key every to the sender and recipient. We will focus on the definition and understand the fundamentals of the sector in this column. Consequently, we’ll take a peek at the varied makes use of of this expertise in real-life scenarios. Most of what cryptographers at analysis Institutes provide you with are proof of concepts.
While they have been effective in their time, they are comparatively easy to interrupt with modern computing energy. Working on developing such cryptographic techniques is Arpita Patra, Assistant Professor at the Division of Pc Science and Automation (CSA), IISc. According to her, cryptography permits secure communications as a result of we reside within the age of data and there is mistrust in this world. In e-commerce, cryptography secures sensitive customer information, similar to https://jdtcindia.com/a-dealer-s-guide-to-fibonacci-trading-methods/ cost data.
To decrease dangers, use sturdy encryption algorithms, secure key administration, and keep safety protocols up to date. After understanding encryption and decryption, it’s time to take a look at the potential risks to cryptographic techniques and the strategies that can mitigate these threats. With instruments like encryption, hashing features, and digital signatures, cryptography permits customers to take part in a system where trust is built into the know-how itself. Every transaction, verification, and replace is recorded in a clear ledger that resists tampering. In the end, the real basis of crypto isn’t solely decentralization—it’s the absolute certainty and security provided by arithmetic.
Cryptography in cybersecurity is crucial for protecting sensitive information and guaranteeing safe communication. Its main targets are confidentiality, integrity, authentication, and non-repudiation, preventing unauthorized access and data manipulation. In cryptography, mathematical ideas and a set of rule-based calculations are often identified as algorithms which are utilized in cryptography to transform messages into ways that make them difficult to decode. Cryptographic key era, digital signing, and verification are all performed with these algorithms to safeguard knowledge privacy, web browsing, and confidential credit card and debit card transactions. Next, focus shifts to asymmetric key cryptography, which makes use of public and private keys for encryption and decryption, providing enhanced security and addressing some challenges posed by symmetric methods.
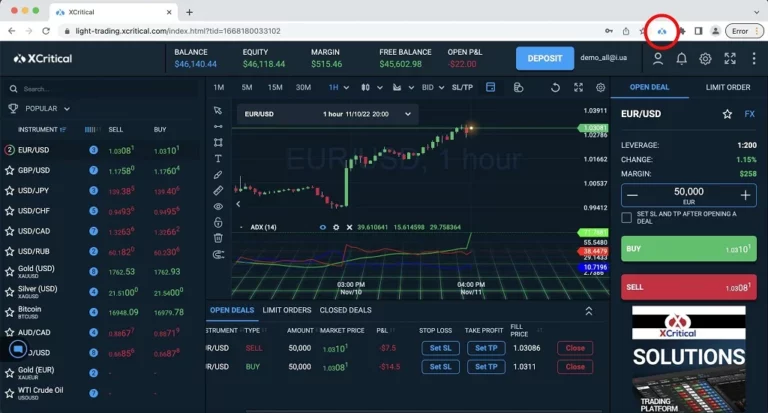
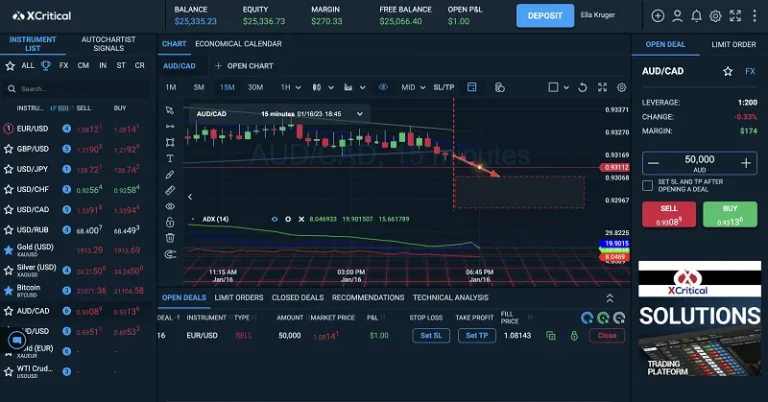
But the Internet’s Achilles’ heel is its open community, making non-public information – searching history, bank account particulars, passwords, bank card info and the like – vulnerable to leaks and manipulation. Cryptography is the science of defending delicate information ̶ identical to satellite areas https://www.xcritical.in/, which can even be of nationwide significance, especially if they’ve army purposes. Maybe if the makers of Iridium 33 and Kosmos 2251 had relied on cryptography, the panorama of outer house would look rather completely different today. Cryptography in cyber security is a popular tool for protecting IT property and offers a quantity of advantages, like confidentiality, information integrity, authentication, and extra. Cryptography holds a major place when it concerns consumer and information safety.
Since everyone thinks the “fake Public key” is the Receiver’s Public key, any messages signed by the intruder utilizing the corresponding “fake Private key” might be accepted as messages sent by the Receiver. Cryptography, not solely protects knowledge from theft or alteration but can additionally be used for consumer authentication. Jaro presents dedicated learner support, live session access, personalized career counseling, and value-added companies through Jaro Connect. Right Here the lady converts the plain text into cipher text using a key which is “C”. The boy will must have this key which he can use to transform the cipher textual content into the plain text.